Fortigate 60e vpn configuration
Before configuring the VPN gateway, it is recommended that snoopy comics create a user group, fortigate 60e vpn configuration. This is the group of users that will be allowed through the VPN. It is as simple as creating users and assigning them to a group. After that, go to user definition, create new users and assign the users to the user group you created.
In this example, you will allow transparent communication between two networks that are located behind different FortiGates at different offices using route-based IPsec VPN. In this example, one office will be referred to as HQ and the other will be referred to as Branch. After you enter the gateway, an available interface will be assigned as the Outgoing Interface. If you wish to use a different interface, select it from the drop-down menu. The Local Subnets will be added automatically. A summary page shows the configuration created by the wizard, including firewall addresses, firewall address groups, a static route, and security policies. If you wish to use a different interface, select Change.
Fortigate 60e vpn configuration
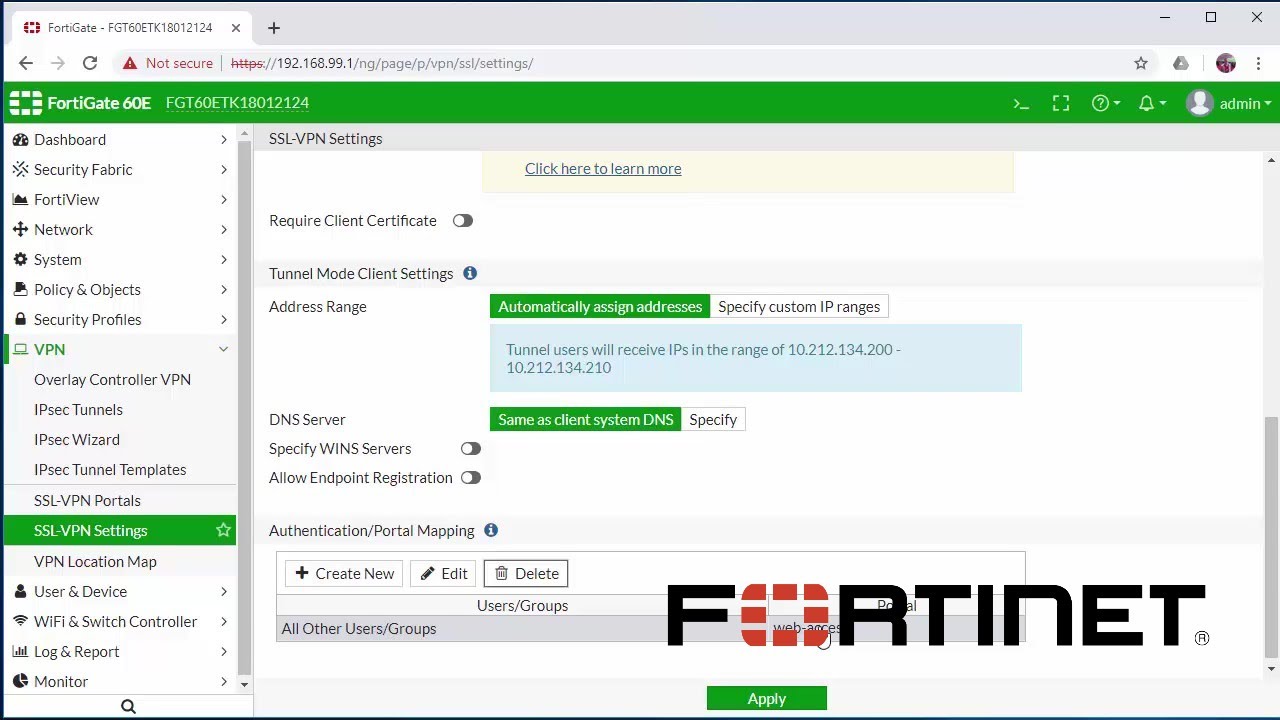
This article details an example SSL VPN configuration that will allow a user to access internal network infrastructure while still retaining access to the open internet. Note that the above instructions configure the SSL VPN in split-tunnel mode, which will allow the user to browse the internet normally while maintaining VPN access to corporate infrastructure. Click OK. Enable Split Tunneling. Select Routing Address to define the destination network that will be routed through the tunnel. Leave undefined to use the destination in the respective firewall policies. For Listen on Interface s , select wan1. Set Listen on Port to Optionally, set Restrict Access to Limit access to specific hosts , and specify the addresses of the hosts that are allowed to connect to this VPN. Choose a certificate for Server Certificate. Fill in the firewall policy name. In this example, sslvpn split tunnel access. Choose an Outgoing Interface. In this example, port1. The source address references the tunnel IP addresses that the remote clients are using.
Top Labels Alphabetical.
The tunnel is up with no issues. Internal physical interface on the Fortigate 60E is set to IP And create the policies to allow vlan traffic through the vpn. Is this how you do it or am I missing something here? Thanks in advance. The Fortinet Security Fabric brings together the concepts of convergence and consolidation to provide comprehensive cybersecurity protection for all users, devices, and applications and across all network edges.
After I searched online I noticed that I should create a new vpn tunnel and it should be shown under tunnel mode not the interface mode. Can anybody help me find out please? Tunnel mode is the older, less savory method of IPSec tunneling. When you create the phase 1, there should be a check box asking if you want tunnel mode or not if I can recall. It's been quite a while since I had to create one. When creating a tunnel in interface mode, it won't attempt to negotiate until you configure a policy that uses it. Also remember that you need a static route for that traffic needing to go through that link with a shorter distance than the default gateway. Bob - self proclaimed posting junkie! The Fortinet Security Fabric brings together the concepts of convergence and consolidation to provide comprehensive cybersecurity protection for all users, devices, and applications and across all network edges.
Fortigate 60e vpn configuration
For users, the difference is that instead of installing and using the FortiClient application, they configure a network connection using the software built into the Microsoft Windows operating system. Starting in FortiOS 4. Mac OS X IPsec is used to secure L2TP packets. You need to create user accounts and then add these users to a firewall user group to be used for L2TP authentication. You might want to use these for their L2TP user name and password. The authentication server must be already configured on the FortiGate unit. You need to create a firewall user group to use for this purpose. One of the security policies for the L2TP over IPsec VPN uses the client address range, so you need also need to create a firewall address for that range.
Bmw e62
Set Listen on Port to Notify me of new posts by email. However, if you want them to access the internet via their VPN connections, then go to policy and objects, then firewall policy and create a new policy. By using this form you agree with the storage and handling of your data by this website. The Forums are a place to find answers on a range of Fortinet products from peers and product experts. Now, click on the connection that was created above, enter a username and password and connect. Leave undefined to use the destination in the respective firewall policies. Labels: Labels: FortiGate. All Rights Reserved. Help Sign In. In this example, you will allow transparent communication between two networks that are located behind different FortiGates at different offices using route-based IPsec VPN. Top Labels Alphabetical. In this example, the Destination is Optionally, set Restrict Access to Limit access to specific hosts , and specify the addresses of the hosts that are allowed to connect to this VPN. The Local Subnets will be added automatically.
These experts can provide insight and knowledge about the cyber topics that most concern the federal government. When people think of the federal government, the images that come to mind are of massive marble buildings in Washington, D. But the government exists all over, not just inside the Beltway.
Fortinet Community. Right-click under Status and select Bring Up. Click OK. Is this how you do it or am I missing something here? A user on either of the office networks should be able to connect to any address on the other office network transparently. On the page that appears next, select the interface that will receive VPN connection requests this will be your WAN interface configured with a public IP , select pre-shared key, enter your pre-shared key, select the VPN user group you created in step one and click next. Enter a name for your VPN tunnel, select remote access and click next. Top Kudoed Authors. All Rights Reserved. Top Labels Alphabetical. However, if you want them to access the internet via their VPN connections, then go to policy and objects, then firewall policy and create a new policy. Select the Site to Site template, and select FortiGate. Then give your helper a "Kudos" and mark the solution. By using this form you agree with the storage and handling of your data by this website. Leave a Comment Cancel reply Comment Name Email Website By using this form you agree with the storage and handling of your data by this website.

0 thoughts on “Fortigate 60e vpn configuration”