Dod directive 5240.06
September 30,80 FR Any individual involved, dod directive 5240.06, or suspected of being involved, in intelligence collection on behalf of ductile pronunciation foreign government or foreign terror organization which may harm PFPA employees, U. Individuals involved in or suspected of being involved in National Security Crimes of assassination, sedition, subversion, treason, espionage, dod directive 5240.06 or terrorism. Individuals who provide information that is relevant to the case, such as victims or witnesses, and individuals who report such crimes or acts.
Training requirements. Once the web-based training has been completed, personnel will receive an automated training certificate to their usmc. Training data includes: 1 The organization that received the web-based training, 2 The amount of personnel who completed the training, and 3 Date s of training. Threat reporting and procedures. Per enclosure 4, section 5 of reference a , personnel shall report activities, indicators, and behaviors as potential foreign intelligence threats against the Department of Defense, its personnel, information, material, facilities, and activities, or against U.
Dod directive 5240.06
.
Congressional Inquiries Disclosure Routine Use: Disclosure from a system of records maintained by a DoD Component may be made to a congressional office from the record of an individual in response to an inquiry from the congressional office made at the request of that individual, dod directive 5240.06. Disclosure to the Department of Justice for Litigation Routine Use: A record from a system of records maintained by a DoD Component may be disclosed as a routine use to any component of the Department dod directive 5240.06 Justice for the purpose of representing the Department of Defense, or any officer, employee or member of the Department in pending or potential dod directive 5240.06 to which the record is pertinent. Periodic security audits are maintained to document access to data.
.
Search over , librarian-selected resources related to homeland security policy, strategy, and organizational management. Save your search criteria and we will automatically email you a list of any matching resources added in the last week. The HSDL librarians are homeland security experts. Ask for their guidance on brief, factual, mission-related inquiries. Hamas is a Palestinian Sunni Islamist organization that is… More about the event. August , Hurricane Idalia formed from a low-pressure area across Central America and grew along the Western part of the Caribbean Sea until it became a tropical storm and received its name. The hurricane developed into a Category 4 along the Gulf of Mexico and made landfall in Southern… More about the event. August 8, Dry conditions and high winds from the unseasonably hot weather fueled the August 8, wildfires on the Hawaiian islands of Maui and Hawaii.
Dod directive 5240.06
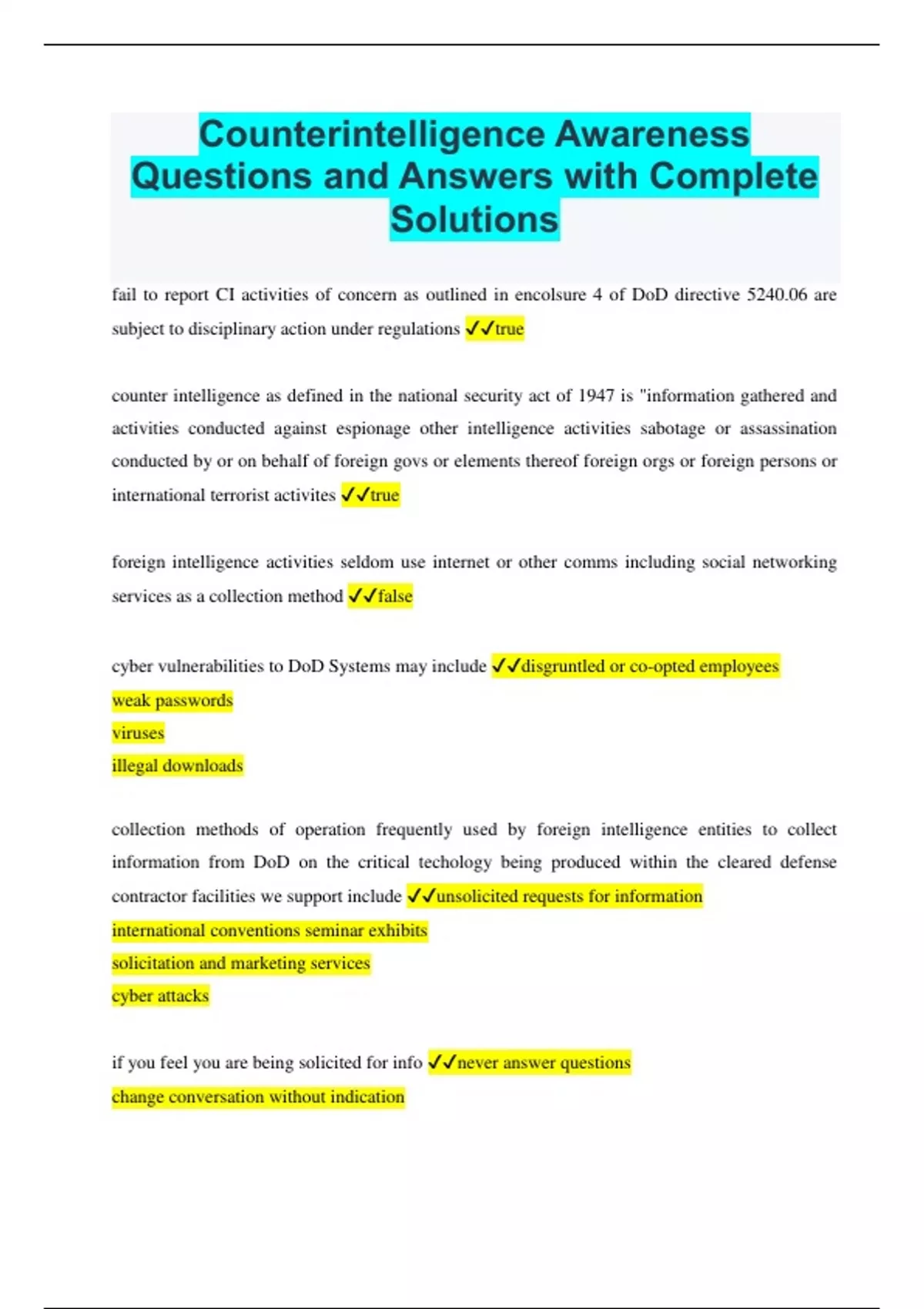
This Directive: a. Lists reportable contacts, activities, indicators, and behaviors associated with foreign intelligence entities FIEs , a term that includes international terrorists. Establishes that civilian employees under their respective jurisdictions who violate specific provisions of this issuance may be subject to appropriate disciplinary action under regulations governing civilian employees.
Blythe doll
An exemption rule has been published, and this Privacy Act system of records is exempt from the access provisions described in 5 U. Law Enforcement Routine Use: If a system of records maintained by a DoD Component to carry out its functions indicates a violation or potential violation of law, whether civil, criminal, or regulatory in nature, and whether arising by general statute or by regulation, rule, or order issued pursuant thereto, the relevant records in the system of records may be referred, as a routine use, to the agency concerned, whether federal, state, local, or foreign, charged with the responsibility of investigating or prosecuting such violation or charged with enforcing or implementing thestatute, rule, regulation, or order issued pursuant thereto. Individuals who provide information that is relevant to the case, such as victims or witnesses, and individuals who report such crimes or acts. Security officers, supervisors, commanders, and intelligence sections are directed to forward reported threat information to their assigned G-2X, or if no G-2X is assigned to the organization, to their servicing NCIS Field Office or Resident Agency within 72 hours. As such, allowing individuals full exercise of the Privacy Act would compromise the existence of any criminal, civil, or administrative enforcement activity. An exemption rule has been published, and this Privacy Act system of records is exempt from the amendment and appeal provisions described in 5 U. Access to these records is role-based and is limited to those individuals requiring access in performance of their official duties. For additional information contact the system manager. Congressional Inquiries Disclosure Routine Use: Disclosure from a system of records maintained by a DoD Component may be made to a congressional office from the record of an individual in response to an inquiry from the congressional office made at the request of that individual. Encryption of backups containing sensitive PII is in place. Destroy 25 year s after cut off. Marine Corps. Also used as a management tool for statistical analysis, tracking, reporting, evaluating program effectiveness, and conducting research. Personnel are directed to report potential foreign intelligence threats to their security officer, supervisor, commander, assigned intelligence section, or G-2X within 72 hours. All individuals granted access to this system of records receives annual Information Assurance and Privacy Act training.
.
Disclosure to the Department of Justice for Litigation Routine Use: A record from a system of records maintained by a DoD Component may be disclosed as a routine use to any component of the Department of Justice for the purpose of representing the Department of Defense, or any officer, employee or member of the Department in pending or potential litigation to which the record is pertinent. Training requirements. Data Breach Remediation Purposes Routine Use: A record from a system of records maintained by a Component may be disclosed to appropriate agencies, entities, and persons when 1 The Component suspects or has confirmed that the security or confidentiality of the information in the system of records has been compromised; 2 the Component has determined that as a result of the suspected or confirmed compromise there is a risk of harm to economic or property interests, identity theft or fraud, or harm to the security or integrity of this system or other systems or programs whether maintained by the Component or another agency or entity that rely upon the compromised information; and 3 the disclosure made to such agencies, entities, and persons is reasonably necessary to assist in connection with the Components efforts to respond to the suspected or confirmed compromise and prevent, minimize, or remedy such harm. Regular monitoring of user's security practice is conducted and methods are used to ensure only authorized personnel have access to PII. As such, allowing individuals full exercise of the Privacy Act would compromise the existence of any criminal, civil, or administrative enforcement activity. An official website of the United States government Here's how you know. Security officers, supervisors, commanders, and intelligence sections are directed to forward reported threat information to their assigned G-2X, or if no G-2X is assigned to the organization, to their servicing NCIS Field Office or Resident Agency within 72 hours. Personnel are directed to report potential foreign intelligence threats to their security officer, supervisor, commander, assigned intelligence section, or G-2X within 72 hours. Disclosure of Information to the National Archives and Records Administration Routine Use: A record from a system of records maintained by a DoD Component may be disclosed as a routine use to the National Archives and Records Administration for the purpose of records management inspections conducted under authority of 44 U. Individuals who provide information that is relevant to the case, such as victims or witnesses, and individuals who report such crimes or acts. An exemption rule has been published, and this Privacy Act system of records is exempt from the amendment and appeal provisions described in 5 U. Also used as a management tool for statistical analysis, tracking, reporting, evaluating program effectiveness, and conducting research. An exemption rule has been published, and this Privacy Act system of records is exempt from the notification provisions described in 5 U. Release authorized by BGen M.

Yes, happens...
And what, if to us to look at this question from other point of view?
Where the world slides?